Major vulnerabilities were discovered in the commonly used Remote Desktop Protocol. A total of 25 RDP vulnerabilities were revealed, with 16 of them considered major vulnerabilities. Vulnerabilities were found in FreeRDP - an open-source RDP, rdesktop - another open-source RDP, and mststc.exe – Microsoft's built-in RDP.
This blog post will cover:
- What is the RDP protocol?
- Vulnerabilities in Microsoft RDP.
- RDP clipboard vulnerability.
- How to mitigating RDP clipboard vulnerability?
What is the RDP protocol?
Remote Desktop Protocol (RDP) is a secure network communication protocol designed for remote access and management to virtual desktops, applications, and RDP terminal servers. It is mainly used by technical users to connect to a remote machine. It is considered a complex protocol – it contains complex features, and therefore might be prone to vulnerabilities.
Vulnerabilities in Microsoft's RDP
Check Point researchers investigated all 3 RDP types. After investigating each protocol's vulnerabilities, Microsoft's RDP was discovered to be the one with the least amount of vulnerabilities. The main vulnerability in Microsoft's RDP is related to the RDP clipboard and its "copy & paste" feature.
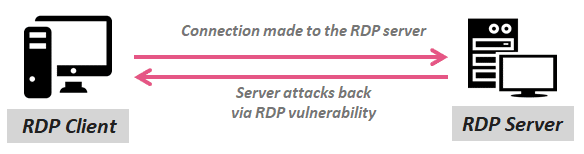
This kind of attack is different from the usual attack vectors and is considered as a reverse RDP attack. Typical RDP attack vectors would use an RDP client in order to connect to a remote RPD server that is installed on the remote computer. However, RDP reverse attacks originate in the remote malicious server, eventually gaining control over the RDP client's computer.
Understanding RDP clipboard
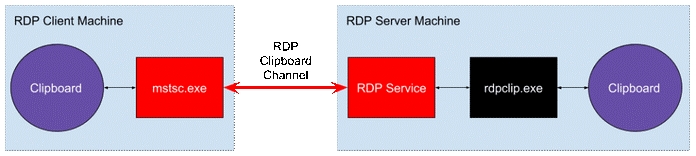
Microsoft's clipboard sharing channel supports several data formats such as CF_HDROP that is responsible for the "Copy & Paste" feature. When used, it allows to simply copy a group of files from one computer to the other. If the client itself fails to prevent malicious files from entering his computer via this feature, he could be vulnerable to a path traversal attack. The server can then drop malicious files in arbitrary paths on the client's computer. In other words, the client's approval of the files is the only thing protecting him from this vulnerability. Considering the fact that the client doesn't even need to verify the received files coming from the RDP server, it is almost impossible to detect the attack.
When initiating a demo attack, Check Point researchers killed the rdpclip.exe port at the RDP server and replaced it with their own process that enabled adding an additional malicious file to every "Copy & Paste" action. There's usually no need for any elevated permissions in order to perform the attack.
Microsoft's response:
Microsoft approved the vulnerability but announced it won't be covered as part of their services.
"Thank you for your submission. We determined your finding is valid but does not meet our bar of servicing".
Therefore, this vulnerability has no CVE-ID and no patch to solve it.
What can be done:
Obviously, the easiest way to approach this vulnerability is to disable this function. Disabling it via a native configuration tool such as GPO is a rather time-consuming and labor demanding approach. Moreover, it can also lead to production damage if you disable it when it is actually needed. The proper way to address this issue is via automated tools such as CalCom's automated hardening software.
If you've decided that some users do need the clipboard function enabled, it is recommended to segment the LANs that have RDP clipboard enabled, so they can be tracked. CalCom's dashboard will show a clear picture of your vulnerabilities, making sure that they are all confirmed and consciously decided.
https://gbhackers.com/rdp-attack-critical-vulnerabilities/
https://research.checkpoint.com/reverse-rdp-attack-code-execution-on-rdp-clients/
https://www.itnews.com.au/news/remote-desktop-clients-analysed-and-found-vulnerable-518908
https://securityaffairs.co/wordpress/80720/hacking/reverse-rdp-attack.html
https://community.spiceworks.com/topic/1077488-rdp-exploits