Docker containers are becoming more and more popular in organizations IT environments because they allow virtualization at the operating system level. Currently, the most common OS for Docker hosting is Linux OS, due to special features that best feat to Docker's need from its host.
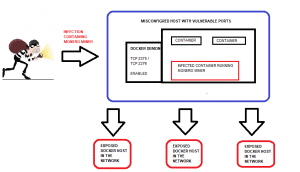
A new infection was found that hunts for misconfigured publicly exposed Docker services. The virus infects the services with containers that run Monero miners.
Entry point:
Docker services use REST API to enable its management tools to perform actions such as creating new containers and starting/stopping them. Default configurations only allow Unix socket to access Docker's REST APIs. In order to enable remote access to the REST API, Docker daemon needs to be configured to listen on TCP ports. The ports usually listened by Docker are 2375 and 2376 which provide unencrypted and unauthenticated access to the Docker REST API by default.
Docker APIs allow remote users to control the Docker images in the same fashion a local user would. So eventually when opening the API port for external access using the unprotected PORT, hackers might abuse it for malicious activities.
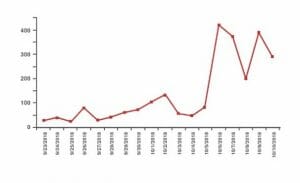
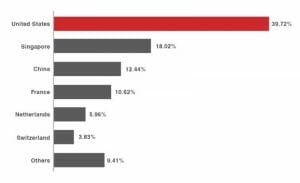
Misconfigurations in a manually set up at the administrator level are an eternal challenge for organizations. Research revealed that many organizations still had their Docker hosts misconfigured. Furthermore, at the end of 2018 numbers were still very high in countries such as the U.S, France, Germany, Singapore, Netherlands, United Kingdom, Japan, India, and Ireland. The majority of the exposed organizations run on Linux OS, using relatively recent Docker released/version.
Spreading method:
The infection spreads using misconfigured Docker services with TCP ports 2375 and 2376 enabled. Every new infection continues to spread to other hosts by scanning for more misconfigured Docker hosts on the network. The infection spreads automatically using scripts and utilities on the targeted system- a 'living off the land' spreading tactic. Among the scripts, which are being utilized are Docker, wget, cURL, Bash, iproute2, MASSCAN, apt-get, yum, up2date, Pacman, dpkg-query, and systemd.
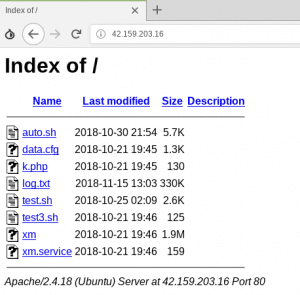
Once the attacker reaches a vulnerable Docker host OS, they start a container and use it to download and lunch 'auto.sh.' 'auto.sh' is a script responsible for both extending the operation and starting the Monero mining job, by executing the MoneroOcean's mining script.
In order to spread to other hosts, the 'auto.sh.' the script also downloads any package, which is missing for it to continue proliferating. 'test.sh' and 'test3.sh' scripts are used to process the text file that contains all IP addresses of the misconfigured Docker daemons. The scripts loop through each IP address on the list and connect to their remote hosting, using Docker's client tool.
'auto.sh.' the script also downloads any package, which is missing for it to continue proliferating
What should you do?
Reaching remotely through the network to Docker in a more secure fashion can be easily achieved by running communication over TLS protocol. When using TLS, the Docker daemon accepts only authenticated connections with a trusted certificate. In order to enable TLS, make sure that 'tlsverify' flag is enabled and defining a trusted certificate for the 'tlscacert' flag.
Misconfigurations leading services to be exposed to the public internet are a gift to hackers of any kind. Cryptocurrency mining is only one of the risks organizations face when using containers in their IT system.
Linux OS is believed to be more secure than other OS, but it is probably because up until now it was a less strategic target for attackers. As Linux usage spreads, most likely due to the virtualized technologies that find it more suitable to their needs, attacks will raise. Security professionals know there is no OS more secure than the other.
CHS for Linux by CalCom will solve this challenge for you by automating your hardening process. With CHS' learning ability, hardening actions will be conducted without the need to invest in lab testing and without causing any outages to production. Also, configurations will be updated according to best practices and recommendations and will be automatically implemented on production environment in one simple action. Using CHS for Linux will give you the ability to get updates regarding your state of compliance constantly.
References:
https://www.theregister.co.uk/2017/07/28/malware_docker_containers/
https://www.bleepingcomputer.com/news/security/misconfigured-docker-services-actively-exploited-in-cryptojacking-operation/